Businesses are moving faster than ever—cloud apps, remote work, new vendors, and always-on customer engagement across websites and social media. That speed increases exposure. This article is a practical approach designed to strengthen security posture by finding what matters, proving what’s exploitable, and fixing issues that create real business impact.
CTEM is not “more scanning.” It is a threat exposure management program that connects security work to outcomes: protecting revenue, uptime, reputation, and customer trust. Instead of drowning security teams in noise, CTEM helps leaders understand the attack path most likely to succeed, how existing security is performing, and which actions will reduce risk in measurable ways.
Why Traditional Vulnerability Management Is Failing Businesses
Classic vulnerability management was built for a simpler world: a known network perimeter, a smaller tool stack, and slower change. Today, the external attack surface management easm challenge is constant—new subdomains, SaaS services, exposed APIs, and misconfigurations appear weekly. Point-in-time scans cannot keep up with continuous threat exposure, and “patch everything” is not realistic.
What is CTEM? Defining the Proactive Cybersecurity Paradigm
So, what is ctem? Continuous threat exposure management is a continuous monitoring discipline that combines discovery, risk management, threat intelligence, and real-world testing. The goal is to understand identified exposures in context—what is reachable, what is exploitable, and what creates the highest potential impacts—then drive a repeatable cycle of improvement that aligns security with business priorities.
Benefits of Continuous Threat Exposure Management
The benefits of continuous threat exposure management go beyond better dashboards. A mature ctem program creates clarity: which exposures matter, why they matter, and what to do next. It also improves collaboration, because security controls are evaluated against real attack behavior rather than theoretical checklists.
Reduced Cyber Risk and Breach Probability
CTEM focuses teams on exposures that attackers can actually use. By validating exploitability and mapping risk to an attack path, the program reduces guesswork and accelerates remediation. When your process consistently prioritizes exposures that create real entry points, you reduce risk faster than a backlog-driven patch cycle.
Better Security ROI
Security spending should not be measured by tool count. CTEM improves ROI by showing where investments work and where they do not. When validation proves which security controls block common tactics—and which gaps remain—you can shift budget toward what measurably lowers exposure and prevents costly incidents.
Improved Visibility Across Attack Surfaces
Modern environments include cloud, endpoints, identity systems, third parties, and customer-facing assets. CTEM improves visibility by connecting internal findings with internet-facing realities, including EASM signals. Teams gain a clearer view of how assets link together, where shadow IT lives, and where exposures cluster across business units.
Stronger Compliance and Governance
Compliance programs often struggle to reflect real risk. CTEM strengthens governance by tying remediation to business criticality, documenting decisions, and proving that controls are tested. That evidence supports audits while also improving operational discipline—because “fixed” means verified, not assumed.
The 5-Stage CTEM Lifecycle: A Continuous Loop
The core stages of the ctem framework form a loop, not a one-time project. Each cycle turns raw findings into action, then measures results to refine the process. This is where CTEM differs from traditional vulnerability management: it is built to be repeatable, adaptive, and outcome-driven.
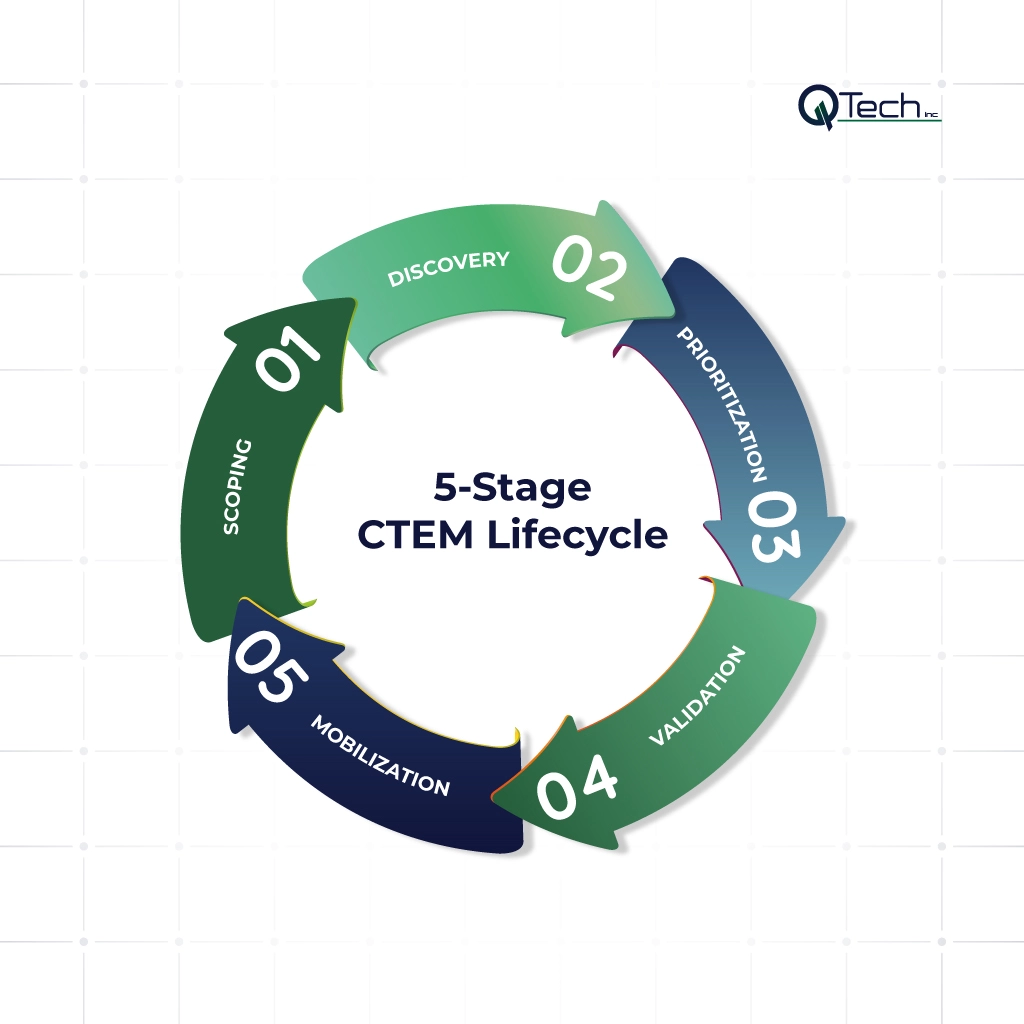
Stage 1: Scoping – Defining Your Digital Attack Surface
Scoping defines what matters most: crown-jewel systems, critical apps, key identities, and high-value data flows. It also defines the business impact of failure—downtime, regulatory exposure, brand damage, and customer churn. Effective scoping ensures the program aligns security to priorities instead of scanning “everything equally.”
Stage 2: Discovery – Identifying Assets & Exposures
Discovery inventories assets across cloud, on-prem, endpoints, and internet-facing properties, then surfaces identified exposures. This includes misconfigurations, outdated services, weak authentication paths, and vendor-related risks. Discovery should be continuous because the environment changes daily, and blind spots are where attackers thrive.
Stage 3: Prioritization – From Thousands of Alerts to a Critical Few
Prioritization converts volume into focus. A strong CTEM approach prioritizes exposures based on exploitability, reachability, and business criticality—rather than severity scores alone. The result is a short, defensible list of fixes that security teams can execute, track, and communicate to leadership with confidence.
Stage 4: Validation – Confirming What’s Actually Exploitable
Validation is the proving ground. This stage uses safe testing methods—such as attack simulation and controlled exploitation checks—to confirm what is actually exploitable and what is not. Solutions like Cymulate ctem can support this style of evidence-driven testing, helping teams understand real attacker behavior without waiting for a breach.
Stage 5: Mobilization & Improvement – Driving Action & Refining Process
Mobilization turns insight into outcomes: tickets, ownership, SLAs, and follow-through. It also drives improvement by measuring what changed after fixes, tuning controls, and eliminating recurring exposure patterns. Over time, CTEM becomes a threat exposure management ctem operating rhythm that strengthens resilience as the business evolves.
How Businesses Can Implement CTEM Successfully
Successful ctem implementation requires more than selecting tools—it requires operating discipline. Organizations should define governance, workflows, and accountability so remediation happens quickly and stays aligned to business priorities. When CTEM is integrated with IT operations, it becomes a practical system for continuous improvement, not a side initiative.
Aligning CTEM With Business Objectives
Start by defining outcomes leadership cares about: protecting revenue, reducing downtime, securing customer data, and safeguarding brand trust. Translate those outcomes into scoped assets and measurable targets. When CTEM aligns security to business objectives, reporting becomes clearer and executive support becomes easier to sustain.
Choosing the Right Security Tools
Choose tools that support continuous monitoring, validation, and workflow integration. Look for capabilities that map exposures to attack paths, test security controls, and provide actionable context.
Partnering With Cybersecurity Experts
Many businesses need help operationalizing CTEM across IT and security. A partner can help standardize discovery, tuning, prioritization logic, and response processes—especially when teams are lean. If your CTEM effort depends on fast remediation and stable systems, pairing it with managed IT services for businesses supports execution, patching, and operational consistency.
Conclusion: CTEM — The Future of Cybersecurity with Q-Tech Inc.
CTEM is a practical shift: from reactive cleanup to continuous threat exposure reduction that is measured, validated, and improved. By focusing on the core stages of the ctem framework—scoping, discovery, prioritization, validation, and mobilization—organizations gain clarity on risk, improve governance, and protect the digital experiences customers rely on. With Q-Tech Inc., businesses can build a CTEM-driven posture that strengthens trust, supports growth, and reduces the likelihood of costly security events.
FAQ
Q: What is Continuous Threat Exposure Management (CTEM) in simple terms?
A: CTEM is a proactive cybersecurity approach that continuously identifies, prioritizes, and addresses the vulnerabilities and misconfigurations attackers are most likely to exploit. Unlike old methods that just scan for flaws, CTEM focuses on understanding the business risk of each exposure and validating which ones are truly dangerous, ensuring teams fix the most critical issues first.
Q: How is CTEM different from traditional Vulnerability Management?
A: Traditional Vulnerability Management is often a periodic, reactive process focused on scanning, generating large lists of flaws, and patching based on severity scores alone. CTEM is continuous and proactive. It considers your specific business context, asset criticality, and real-world exploitability to prioritize actions that actually reduce risk, not just the number of vulnerabilities.
Q: What are the core stages of a CTEM program?
A:As outlined by leading frameworks, a mature CTEM program follows a five-stage lifecycle:
- Scoping: Mapping your entire digital attack surface.
- Discovery: Continuously finding assets, vulnerabilities, and exposures.
- Prioritization: Ranking risks based on business impact and threat intelligence.
- Validation: Testing to confirm if exposures are genuinely exploitable.
- Mobilization: Driving remediation and improving processes based on feedback.
Q: What role does automation play in CTEM?
A: Automation enables continuous discovery, validation, and response, making CTEM effective in fast-changing IT environments.






