From smart thermostats in office buildings to internet-connected MRI machines, the Internet of Things IoT is now embedded in how modern businesses operate. Every connected device adds convenience, automation, and new data processing opportunities—but it also expands your attack surface and introduces fresh security risks.
This article is your IoT cybersecurity: a proactive guide to protecting interconnected devices and networks. We’ll break down the biggest cybersecurity challenges in IoT, explain common IoT cyber attacks in plain language, and walk through practical IoT security best practices you can start applying right away. The goal is simple: help you protect sensitive data, keep critical operations running, and build long-term resilience around your IoT systems.
Why IoT Is Revolutionizing Business — and Increasing Cyber Risk
IoT technology has become a quiet engine of digital transformation. Smart sensors, cameras, wearables, and industrial controllers are streamlining workflows, enabling automation, and feeding business intelligence tools with real-time data. But every new connected device can also become a doorway for cyber threats if it isn’t secured properly.
Rapid Growth of Connected Devices
Most organizations already have more IoT devices than they realize. Printers, cameras, point-of-sale terminals, HVAC controllers—almost any modern connected device now “speaks” over the network. As these endpoints multiply, so does your IoT cyber risk.
This rapid growth makes it harder to enforce consistent security measures. Devices from different vendors ship with different security features, lifecycles, and update models. Without a deliberate strategy, you end up with a patchwork environment where some devices are well protected and others quietly expose sensitive information.
New Attack Surfaces in IoT Environments
Traditional networks were easier to defend: desktops, servers, and maybe mobile devices. Today, IoT has pushed your perimeter out to parking lots, remote kiosks, and factory floors. Attackers now target cameras, sensors, and controllers that were never designed with strong security standards in mind.
Each IoT device has its own firmware, services, and ports. If even one is misconfigured or left unpatched, it can be exploited for data breaches, lateral movement, or DDoS attacks against your own infrastructure or others. The result is a constantly shifting landscape of vulnerabilities that demands ongoing attention.
Key Cybersecurity Challenges in IoT
While every organization is different, certain IoT security challenges show up again and again. Understanding these will help you prioritize your defenses.
Default Credentials and Weak Authentication
Too many IoT devices still ship with default passwords like “admin/admin”—and they’re rarely changed. Attackers maintain massive lists of these defaults and run automated scans across the internet connection space, looking for exposed devices.
Weak authentication mechanisms, shared credentials, and a lack of multi-factor authentication make it trivial for attackers to take over cybersecurity for IoT devices. Strong identity and access controls are non-negotiable if you want to reduce IoT cyber risk.
Unpatched Firmware / Software Vulnerabilities
Many IoT vendors ship devices, then move on to the next model. Meanwhile, vulnerabilities are discovered, but security updates might be slow, hard to install, or simply not provided. That leaves organizations running outdated firmware with known exploits.
Because these devices often sit in the background “just working,” it’s easy to forget them—until an attacker uses them as an entry point. A disciplined approach to firmware patching is one of the most important IoT security best practices you can implement.
Insecure Communication Protocols
Some IoT devices still transmit data in clear text over the network. Others rely on weak encryption, outdated TLS versions, or proprietary protocols without proper scrutiny. That makes sensitive data vulnerable to interception, tampering, or impersonation.
When communication isn’t protected end-to-end, attackers can perform man-in-the-middle attacks, inject malicious commands, or quietly siphon off sensitive information. Securing IoT communication channels is vital for robust IoT threat detection and prevention.
Lack of Visibility & Monitoring
You can’t protect what you can’t see. Many organizations lack a complete inventory of their IoT devices, much less visibility into how those devices behave in real time.
Without centralized monitoring, unusual patterns—like a camera suddenly sending large volumes of data to an unknown IP—may go unnoticed. This lack of visibility makes cybersecurity challenges in iot harder to manage and slows down incident response when something goes wrong.
Common IoT Cyber Attacks and Their Impact
Attackers target IoT because it’s often the weakest link. Let’s look at some common IoT cyber attacks and what they mean for your business.
Botnets and DDoS Attacks
One compromised IoT device is bad. Thousands are a weapon. Attackers routinely compromise vulnerable IoT devices and chain them together into botnets used to launch massive DDoS attacks.
Even if your organization isn’t the final target, your devices can be abused to attack others, putting your reputation and potential legal exposure at risk. This is why proactive IoT threat detection and prevention matters, even if you believe your data isn’t “interesting.”
Data Exfiltration and Eavesdropping
IoT devices constantly collect and transmit sensitive data: patient vitals, building access logs, industrial metrics, and more. If those streams are unencrypted or poorly protected, attackers can silently eavesdrop or exfiltrate information.
Over time, this can lead to serious data breaches that expose customers, employees, or proprietary processes. In regulated industries, the financial and compliance impact can be devastating.
Physical World Consequences: Sabotaging Industrial and Medical Systems
Unlike a typical laptop compromise, IoT attacks can have direct physical consequences. Manipulating sensor data in a manufacturing line can damage equipment or degrade product quality. Interfering with medical IoT devices can jeopardize patient safety.
These security risks turn cybersecurity into a safety issue. Protecting IoT isn’t just about data; it’s about preventing real-world harm to people and infrastructure.
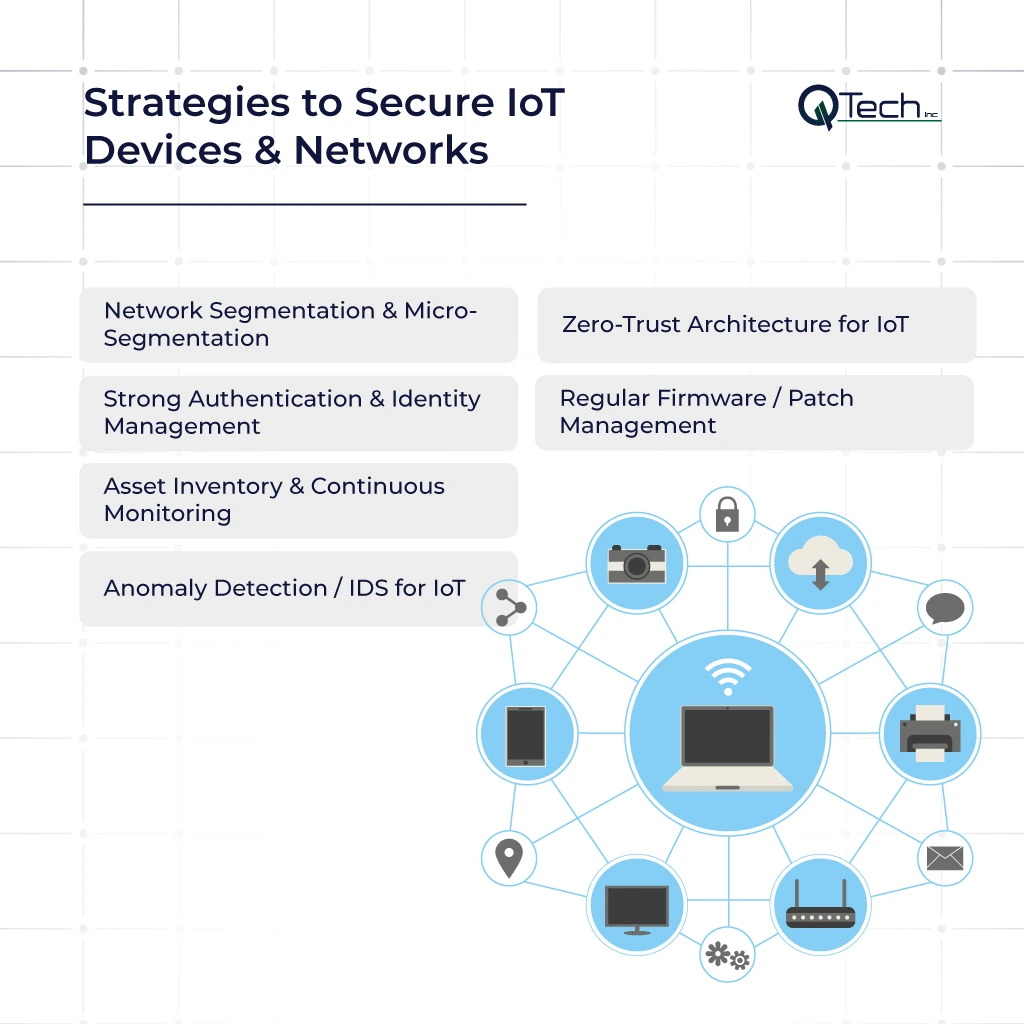
Proactive Strategies to Secure IoT Devices & Networks
A reactive approach is no longer enough. To stay ahead, you need a layered, proactive strategy for securing IoT environments—combining technology, processes, and people.
- Network Segmentation & Micro-Segmentation
- Zero-Trust Architecture for IoT
- Strong Authentication & Identity Management
- Regular Firmware / Patch Management
- Asset Inventory & Continuous Monitoring
- Anomaly Detection / IDS for IoT
Network Segmentation & Micro-Segmentation
Start by ensuring IoT devices never share the same flat network as your critical servers or workstations. Use VLANs and firewalls to segment traffic and, where possible, apply micro-segmentation so each device or group only talks to what it truly needs.
This limits blast radius: if a single connected device is compromised, the attacker can’t easily move deeper into your environment. Segmentation is one of the most cost-effective security measures you can implement.
Zero-Trust Architecture for IoT
Zero-trust assumes no device or user is trustworthy by default—every access request must be verified. Applying this mindset to IoT means enforcing strict access controls, continuous verification, and least-privilege access to services and data.
Combined with your broader enterprise cybersecurity strategy, zero-trust helps ensure compromised devices can’t freely roam across your network. It also aligns with modern security standards and regulatory expectations.
Strong Authentication & Identity Management
Each device should have a unique identity and use strong, non-default credentials. Where possible, deploy certificate-based authentication, role-based access control, and multi-factor authentication for administrative access.
Centralized identity and access management for IoT reduces the risk of shared logins and makes it easier to revoke access quickly when employees leave or roles change. This is foundational to effective cybersecurity for IoT devices.
Regular Firmware / Patch Management
Create a formal process for tracking firmware versions, reviewing vendor advisories, and scheduling updates. Test patches in a controlled environment when possible, then roll them out in phases.
Automated tools and managed IT and monitoring services can help streamline this work, ensuring security updates are applied consistently across your environment without disrupting operations.
Asset Inventory & Continuous Monitoring
Maintain a living asset inventory of all IoT devices: model, firmware version, location, purpose, and owner. Pair this with continuous monitoring that tracks behavior in real time.
When a device suddenly starts communicating with an unfamiliar destination over the internet connection, you want alerts—not surprises. This monitoring also supports efficient incident response and long-term IoT threat detection and prevention.
Threat Detection: Anomaly Detection / IDS for IoT
Traditional intrusion detection systems often miss IoT-specific threats. Modern solutions use behavioral analytics and artificial intelligence AI to learn what “normal” looks like for each device and flag anomalies.
By leveraging artificial intelligence and machine learning tuned to IoT traffic, you can spot subtle indicators of compromise early. This advanced IoT security best practices approach complements segmentation and patching to form a stronger overall defense.
Advanced Security Measures: Emerging Solutions
As IoT complexity grows, so do the tools to protect it. Beyond the basics, some emerging approaches can give you additional resilience.
Trust-Based Security Models for IoT
Trust-based models evaluate each device’s behavior, configuration, and history to assign a dynamic trust score. If a device starts acting suspiciously, its trust score drops, and its access is automatically restricted or revoked.
This adaptive approach helps organizations keep pace with fast-moving cyber threats without manually tuning every rule, and it supports scalable security features across large, distributed environments.
Using Honeypots / Honeynets in IoT
IoT honeypots and honeynets are decoy devices and networks designed to attract attackers. By observing how adversaries behave, you gain valuable intelligence on new IoT security challenges and exploit techniques.
This information can then be used to refine defenses, tune detection rules, and improve enterprise cybersecurity programs across both traditional IT and IoT domains.
Microservices Architecture for IoT Security
Designing IoT security capabilities as modular microservices—such as authentication, logging, and data processing—makes it easier to update, scale, and integrate them.
This modern architecture supports IoT systems that can evolve quickly as new vulnerabilities emerge, helping you maintain strong security measures without constant large-scale redesigns.
IoT in the Cloud: Special Security Considerations
Many organizations now manage IoT in the cloud, using platforms that aggregate data, run analytics, and orchestrate devices remotely. This brings agility—but also new considerations.
Risks in Cloud-Based IoT Systems
Cloud-based IoT platforms centralize large volumes of sensitive data, making them attractive targets. Misconfigurations, weak API security, or poor access controls can expose device data or even allow attackers to issue commands to field devices.
You need a shared responsibility mindset: cloud providers secure the platform, but you remain responsible for identities, data, and configurations. Aligning cloud and IoT strategies is crucial to controlling IoT cyber risk.
Ensuring Data Integrity & Privacy
When IoT data flows to the cloud, you must ensure it’s encrypted in transit and at rest, with strict access controls and logging. Strong key management and tokenization help protect sensitive information even if a breach occurs.
Clear data governance policies, including retention, access, and deletion, are essential for privacy and compliance—especially in regulated sectors that depend on secure Internet of Things IoT deployments.
Measuring Your IoT Security Maturity
You can’t improve what you don’t measure. Mature IoT security programs use metrics and frameworks to track progress and guide investment.
Key Metrics (Vulnerability Rate, Incident Response Time, Device Compliance)
Useful metrics include the percentage of devices on current firmware, mean time to detect and respond to incidents, and device compliance with internal security standards.
Tracking trends in vulnerability counts, patch status, and cybersecurity challenges over time helps leadership see where resources are working—and where additional focus is needed.
Risk Assessment Frameworks
Structured risk assessment frameworks tailored for IoT help you evaluate exposure across people, process, and technology. They consider device criticality, network placement, data sensitivity, and the likelihood of different attack scenarios.
By regularly assessing IoT security challenges, you can prioritize remediation efforts and align them with broader enterprise cybersecurity and compliance goals.
Conclusion: Why IoT Security Matters — and How Q-Tech Inc. Keeps You Ahead
IoT is no longer optional—it’s woven into how modern organizations compete, serve customers, and innovate. But without a clear strategy, that same innovation can create hidden vulnerabilities, from unpatched devices to poorly secured cloud platforms.
Q-Tech Inc. helps businesses turn IoT from a liability into a strength. Our enterprise cybersecurity services and Managed IT and monitoring services are designed to protect interconnected devices and networks end-to-end, combining best-practice architecture, continuous monitoring, and advanced IoT threat detection and prevention.
Whether you’re just starting to inventory your devices or looking to modernize a complex IoT ecosystem, now is the time to act. With the right partner, you can embrace the full potential of IoT while keeping your people, data, and operations secure in an increasingly connected world.
FAQ
Why are IoT devices so vulnerable to cyber attacks?
Answer – IoT devices are inherently vulnerable due to several factors:
- They often ship with default, hard-coded passwords that users never change.
- They frequently lack the computational power for robust security features.
- Many have no secure method for receiving firmware and software updates, leaving known vulnerabilities unpatched for their entire lifespan.
- They use weak or unencrypted communication protocols, making data interception easy.
What is the biggest security risk of IoT devices?
Answer – The single biggest risk is that a compromised IoT device can serve as a backdoor into your entire corporate network. An attacker can use a vulnerable smart thermostat or security camera as a foothold to move laterally, accessing sensitive servers, financial data, and intellectual property. This is why network segmentation is the most critical first step in IoT security.
How can I secure my home or office IoT devices?
Answer – Start with these five essential steps:
- Change all default usernames and passwords to strong, unique ones.
- Segment your network: Place IoT devices on a separate Wi-Fi network (guest network) away from your main computers and phones.
- Disable features you don’t use, like remote administration.
- Regularly check for and install firmware updates from the manufacturer.
- Where possible, choose devices from manufacturers with a strong track record of providing security updates.
What is the difference between IT security and IoT security?
Answer – Traditional IT security focuses on protecting servers, computers, and smartphones—devices with ample processing power, standard operating systems, and built-in security features. IoT security must protect a vast array of constrained, specialized devices (sensors, cameras, controllers) that often lack standard security controls, have long lifecycles, and can have direct physical consequences if compromised, requiring a different, more hardware-focused approach.