In today’s digital-first learning environment, student data security is one of the most pressing challenges schools face. With technology transforming classrooms, educators must safeguard sensitive information against evolving cyber threats. This blog serves as student data security: a complete guide for schools in the digital age, offering practical steps for protecting student information while ensuring compliance with federal law and modern privacy expectations.
Why Student Data Protection Is More Critical Than Ever
Rise of EdTech, remote learning, and data generation
The rapid adoption of EdTech tools, virtual classrooms, and digital assessments has resulted in an unprecedented amount of data collected from students. School districts now handle vast stores of personal identifiers, behavioral data, and students’ educational records. Without proper safeguards, this creates opportunities for unauthorized access and misuse.
Real-world breaches and consequences (e.g., exposed education records)
Recent breaches involving education records highlight the consequences of poor security. When sensitive student information is exposed, schools risk identity theft, academic disruption, and reputational damage. These incidents reinforce why data breach prevention in schools must be a top priority.
Trust, legal liability, reputation risk
Parents entrust schools with their children’s privacy. Failing to protect sensitive student information not only undermines that trust but can also expose institutions to legal liability, fines, and compliance failures. Ultimately, strong data security is essential for maintaining confidence in both schools and the broader education system.
Legal & Regulatory Foundations Schools Must Know
FERPA – access, consent, disclosures, rights
The Family Educational Rights and Privacy Act (FERPA) sets the foundation for student data privacy in the United States. FERPA compliance requires schools to control access to education records, obtain parental consent for disclosures, and protect family educational rights. Schools must implement policies aligned with the FERPA Act mandates to remain compliant.
COPPA, PPRA, others, depending on the region
The Children’s Online Privacy Protection Act (COPPA) and the Protection of Pupil Rights Amendment (PPRA) further establish boundaries for handling student data. Complying with COPPA means ensuring that websites and online services obtain parental consent before collecting information from children under 13. The Coppa rule is a key safeguard to protect children and uphold the Online Privacy Protection Act standards.
Emerging state or regional student privacy laws
Beyond federal law, states are introducing their own student data privacy regulations. School cybersecurity strategies must adapt to this patchwork of requirements. Staying informed about new information practices at state and regional levels is essential for long-term compliance and resilience.
Best Practices for Protecting Student Information
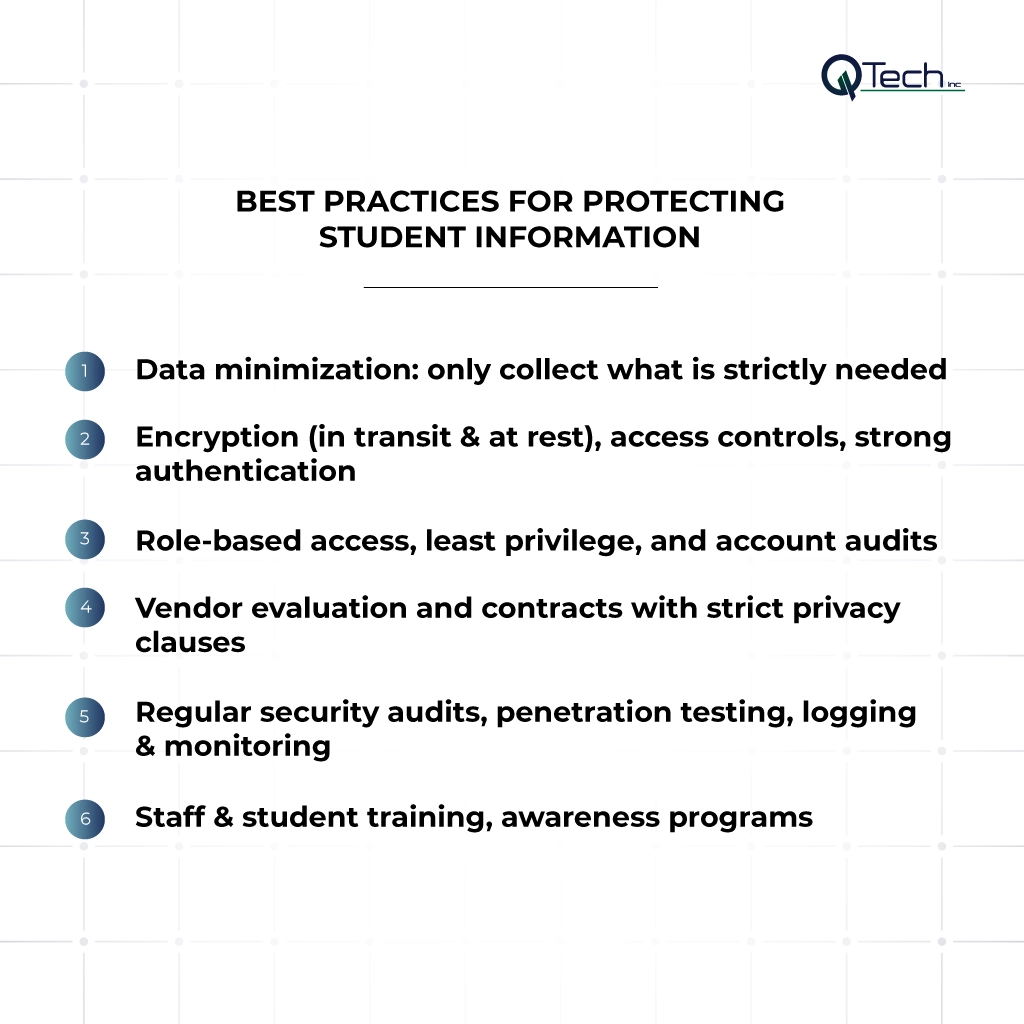
Data minimization: only collect what is strictly needed
Schools should limit the data collected to only what is necessary for educational purposes. This reduces risk and ensures better protection of student information.
Encryption (in transit & at rest), access controls, strong authentication
Implementing student data encryption, robust access controls, and multi-factor authentication helps prevent unauthorized access. Data encryption ensures that even if data is stolen, it remains unreadable without the proper keys.
Role-based access, least privilege, and account audits
Assigning role-based access ensures that only authorized staff can reach sensitive records. Regular account audits help detect misuse and protect sensitive information from insider threats.
Vendor evaluation and contracts with strict privacy clauses
Schools must carefully evaluate EdTech security when working with vendors. Contracts should include privacy clauses, data retention limits, and requirements for complying with COPPA and FERPA.
Regular security audits, penetration testing, logging & monitoring
Proactive school cybersecurity includes regular penetration testing, system monitoring, and audit logs. These practices help identify weaknesses before they become major issues.
Staff & student training, awareness programs
Human error is one of the most common causes of data breaches. Awareness programs help staff and students understand risks, strengthen compliance, and create a culture of data security.
Managing Third-Party EdTech & Vendor Risks
Vendor data policies: retention, sharing, deletion
When using third-party tools, schools must review vendor policies on data retention, sharing, and deletion to ensure compliance with student data privacy standards.
Require clear data usage agreements, non-disclosure, and audits
Strong vendor contracts should include data usage agreements, non-disclosure terms, and audit rights to hold providers accountable.
Ensure third parties comply with student data regulations
Schools must confirm that vendors align with FERPA compliance, COPPA compliance, and other applicable laws. This ensures third parties share responsibility in protecting student data.
Monitor and assess ongoing vendor compliance
Vendor compliance is not a one-time task. Continuous monitoring helps ensure that third parties uphold agreements and remain compliant with school cybersecurity policies.
Emerging Technologies & Privacy-Preserving Approaches
Federated learning & local models to avoid centralizing data
Federated learning allows schools to train models without transferring raw student information to centralized servers, reducing exposure to cyber threats.
Differential privacy, anonymization, pseudonymization
Techniques like differential privacy and anonymization strengthen privacy by masking identifiers. These methods reduce risks while still allowing meaningful data analysis.
Zero-trust models in educational networks
Adopting zero-trust frameworks means schools treat every user, device, and system as potentially untrusted. This strategy minimizes risks from both internal and external actors.
Implementation Roadmap for Schools & Institutions
Inventory & map all student data flows
Schools should begin by mapping all data collected across systems, vendors, and platforms. This provides clarity on where vulnerabilities may exist.
Gap analysis vs legal / best practice baseline
Conduct a gap analysis against federal law requirements, industry standards, and best practices for school cybersecurity.
Prioritize fixes (high risk first)
Address the most critical vulnerabilities, such as a lack of encryption or weak authentication, to reduce exposure quickly.
Deploy security & privacy enhancements
Implement stronger data security solutions, including multi-factor authentication, data encryption, and strict privacy policies for schools.
Monitor, review, iterate
Security is an ongoing process. Schools should regularly review controls, monitor for cyber threats, and update practices to keep pace with evolving risks.
Conclusion: How Q-Tech Inc. Can Help in Protecting Student Data
Safeguarding student data requires a multi-layered approach that combines technology, training, and compliance. At Q-Tech Inc., we specialize in student data security and provide managed IT infrastructure for educational institutions to help schools protect sensitive data, comply with regulations, and build trust with families. By working together, schools and IT experts can ensure students’ educational records remain secure in the digital age.
FAQ
What is FERPA and what student information does it protect?
Answer – The Family Educational Rights and Privacy Act (FERPA) is a federal law that protects the privacy of student education records. This includes all records directly related to a student and maintained by an educational agency, such as grades, transcripts, class schedules, and disciplinary records. It gives parents certain rights to these records, which transfer to the student when they turn 18 or attend a school beyond high school.
What should a school do immediately after a data breach?
Answer – A school should activate its incident response plan, which should include:
- Containing the breach to prevent further data loss.
- Assessing the scope and determining what data was exposed.
- Notifying affected families and legal authorities as required by law.
- Providing credit monitoring or identity theft protection if sensitive data was exposed.
- Conducting a post-incident review to prevent future breaches.
How often should educational institutions audit their student data practices?
Answer – Regularly — ideally quarterly or biannually. Also audit immediately after changes (new tools, vendors, infrastructure). Always review logs, access, compliance gaps, and incident response plans.
Can an off-site IT team manage our school’s data security effectively?
Answer – Yes. For many institutions, particularly those with budget constraints, a Managed IT Services provider is a cost-effective and highly effective solution. They provide 24/7 monitoring, real-time threat detection, and continuous patching that a small in-house team cannot easily maintain.