Introduction: Why Cloud Security Is Critical for Data Protection
Businesses rely on the cloud for speed, flexibility, and scale, but those benefits come with real security responsibilities. Whether your company uses software-as-a-service, collaboration platforms, off-site storage, or infrastructure in public clouds, the risk of data loss never disappears just because systems are hosted elsewhere.
In fact, the phrase vital cloud security tips 2026 protecting your business from data loss is more than a headline. It reflects a practical reality: modern operations depend on securing identities, workloads, applications, and data every day. Strong cloud security tips and disciplined cloud security best practices 2026 help organizations reduce downtime, prevent a data leak, and protect the sensitive information that keeps the business moving.
Definition of Cloud Security
Cloud security is the set of policies, controls, technologies, and habits used to protect data, applications, and services in a cloud environment. NIST defines cloud computing as on-demand access to a shared pool of configurable computing resources, which means security must cover identities, storage, networks, and applications across many moving parts.
In practical terms, that includes access control, encryption, monitoring, backup planning, and clear accountability under the shared responsibility model. Whether a business uses one cloud computing service or several, cloud security is what keeps computing power and business continuity from becoming liabilities instead of advantages. For businesses exploring cloud computing, security must be part of the design from the start, not added after deployment.
Top Causes of Data Loss in Cloud Environments
Data loss in the cloud usually does not come from one dramatic event. It often results from a chain of small weaknesses: poor permissions, weak backups, missed alerts, delayed patching, or one rushed configuration change. The cloud gives organizations flexible computing resources, but that same flexibility can expand risk when security discipline falls behind growth. Companies that treat cloud protection as a one-time setup rather than a living program often discover problems only after business data has been exposed, deleted, encrypted, or corrupted.
Human Error and Misconfigurations
Human error remains one of the most common causes of cloud incidents. A storage bucket left open, overly broad permissions, an exposed API, or a rushed deployment can create gaps that attackers quickly exploit. CISA has warned that misconfigured cloud services are common targets for cyber actors because they can lead to theft of sensitive information and unauthorized use of resources. This is especially important for businesses managing multiple platforms, remote teams, and fast software development cycles, where a small oversight can turn into major data loss.
Cyberattacks and Ransomware
Ransomware, credential theft, and other attack vectors continue to threaten cloud-hosted data. Attackers do not always need to break through a firewall anymore. They often go after identities, tokens, exposed services, or weak admin controls.
Once inside, they can encrypt files, exfiltrate records, or move laterally across connected systems. NIST and CISA both emphasize that data loss incidents tied to ransomware can have catastrophic business effects, especially when recovery planning and isolation controls are weak.
Weak Access Controls
Weak access controls are another major cause of cloud exposure. When users have more permissions than they need, when service accounts are not reviewed, or when passwords are the only defense, risk rises fast.
NIST’s zero trust guidance and CISA’s cloud guidance both stress least privilege and continuous authorization review because excessive access gives attackers more room to operate after a single compromise. Strong identity governance is not optional in cloud environments. It is one of the clearest ways to reduce preventable data loss.
Lack of Backup Strategies
A company may believe its cloud provider is handling everything, only to discover that deleted data, corrupted files, or encrypted workloads cannot be restored the way it expected. That is where weak backup planning becomes dangerous. NIST recommends conducting, maintaining, and testing backups because data loss can result from ransomware, hardware failure, or accidental destruction. Effective cloud backup and recovery depend on having copies that are available, validated, and protected from the same event that damages production systems.
Vital Cloud Security Tips to Prevent Data Loss
- 1. Use Strong Identity and Access Management (IAM)
- 2. Enable Multi-Factor Authentication (MFA)
- 3. Encrypt Data at Rest and in Transit
- 4. Implement Data Loss Prevention (DLP) Tools
- 5. Regularly Monitor and Audit Cloud Activity
- 6. Keep Systems Updated and Patched
- 7. Follow the 3-2-1 Backup Strategy
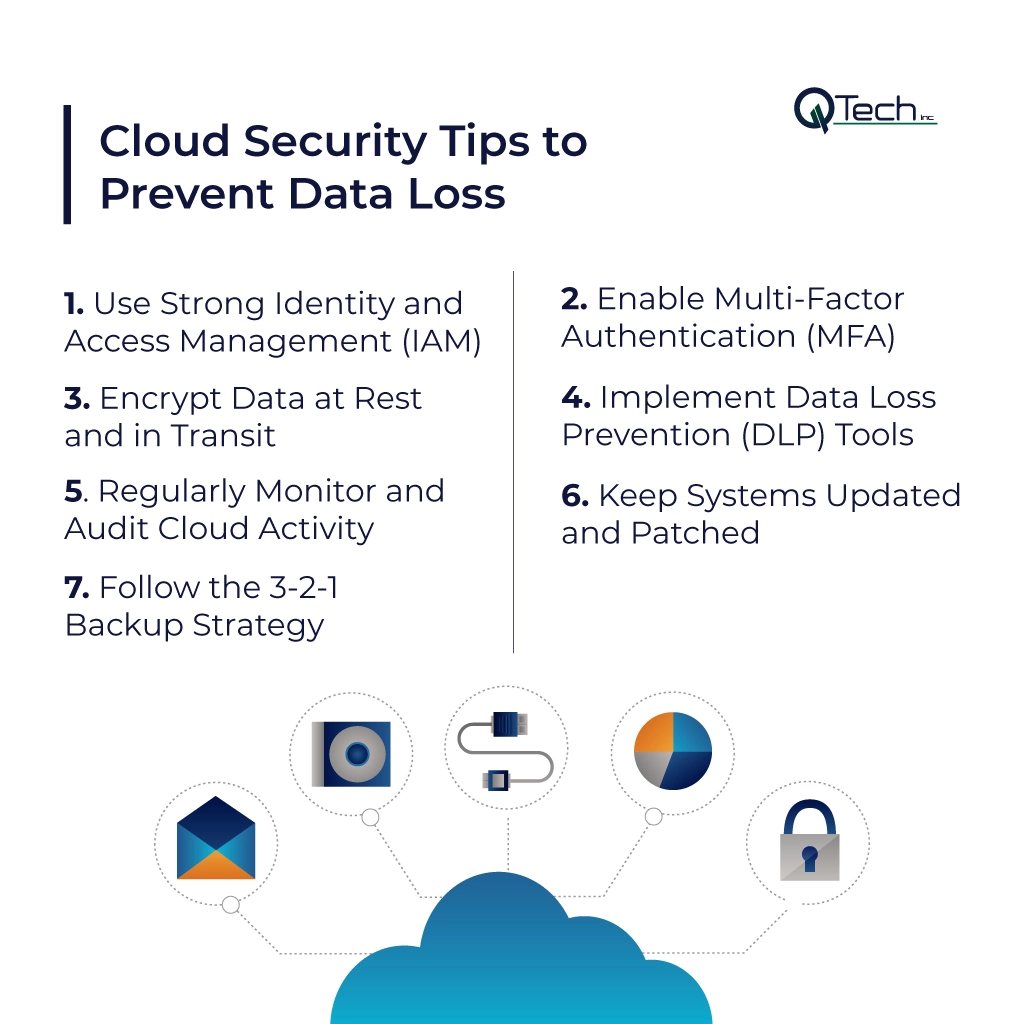
Preventing data loss is not about chasing every possible threat. It is about building layers of control that work together. The most effective cloud security tips focus on identity, verification, encryption, visibility, configuration discipline, and tested recovery. When those controls are aligned, businesses can reduce risk without slowing down daily operations.
Use Strong Identity and Access Management (IAM)
Identity and Access Management is the backbone of secure cloud operations. Every employee, contractor, administrator, workload, and API should have clearly defined access based on role and business need.
Least privilege should apply to human users and machine identities alike. That includes every service saas dashboard, admin account, and integration token. Well-structured IAM limits how far an incident can spread and helps ensure users only reach the data and functions required to do their jobs.
Enable Multi-Factor Authentication (MFA)
Multi-factor authentication is one of the fastest and highest-value improvements a business can make. CISA states that MFA helps prevent unauthorized access by requiring more than a password, and it continues to promote phishing-resistant methods such as FIDO/WebAuthn where possible. For companies using email, admin portals, remote access tools, and software as a service platforms, multi-factor authentication should be mandatory for privileged users and strongly enforced across the organization. Among all saas security tips, this is one of the simplest and most effective.
Encrypt Data at Rest and in Transit
Encryption protects data both when it is stored and when it moves between systems, users, or services. That matters in hybrid work, API integrations, backups, and multi-cloud environments where information travels constantly. NIST guidance continues to support strong encryption for stored data, tokens, and data in transit, including current transport protections such as TLS. Encryption does not replace access control, but it adds another important layer that helps reduce exposure if other safeguards fail.
Implement Data Loss Prevention (DLP) Tools
A strong data loss prevention program gives businesses visibility into where sensitive information lives, how it moves, and when it is being shared in risky ways. Microsoft and Google both describe DLP capabilities as tools to discover, classify, monitor, and protect sensitive data across cloud apps, endpoints, and web traffic. A well-designed data loss prevention dlp strategy can help stop accidental oversharing, enforce policy, and support a more mature dlp solution across email, collaboration tools, storage, and unmanaged cloud destinations.
Regularly Monitor and Audit Cloud Activity
You cannot protect what you do not watch. Logging, alerting, and audit reviews help businesses detect unauthorized changes, suspicious sign-ins, risky privilege changes, and signs of a developing incident. CISA guidance for cloud and ransomware defense emphasizes enabling logging for control plane actions, end-user logins, and changes to IAM or data protection settings. Regular auditing turns cloud security from a static checklist into an active defense program.
Keep Systems Updated and Patched
Cloud systems still depend on software, and software still needs maintenance. Vulnerabilities in applications, workloads, APIs, plugins, and supporting tools can create openings for attackers if updates lag. Even in managed environments, businesses remain responsible for portions of configuration and patching under the shared responsibility model. Mature patch management, combined with secure software development practices, reduces known weaknesses before they become exploitable entry points.
Follow the 3-2-1 Backup Strategy
The 3-2-1 approach remains a practical way to think about resilience: keep multiple copies of data, use more than one storage medium, and maintain at least one protected copy separated from production.
While every business may adapt the exact design, the core principle matches NIST and CISA guidance: backups should be planned, maintained, tested, and isolated enough to remain useful during ransomware or system failure. A cloud backup plan is only valuable when restoration is tested and recovery objectives are clear.
Cloud Data Protection Strategies for Businesses
Tactical controls matter, but long-term protection requires a bigger strategy. Businesses need security models that reflect how modern work actually happens: users connecting from anywhere, applications spread across platforms, and data moving across endpoints, vendors, and cloud services. The goal is not to eliminate all risk. It is to reduce blast radius, improve detection, and recover quickly when issues happen.
Zero Trust Security Model
Zero-trust cloud security is built on one core idea: no user, device, or workload should receive implicit trust just because it is already inside the environment. NIST defines zero trust as a model that focuses on protecting users, assets, and resources rather than assuming the network perimeter is enough.
In that sense, trust is a security decision that must be earned continuously. Businesses implementing zero trust should verify identity and context at every step, enforce granular access, and build a trust architecture that limits lateral movement when accounts or systems are compromised.
Secure Cloud Configurations
Secure configurations reduce avoidable exposure. That means hardening default settings, closing unused services, reviewing public access, separating duties, and validating permissions across every cloud workload.
It also means understanding the shared responsibility model, so teams know which controls belong to the provider and which belong to the customer. In many cases, the biggest risk in cloud computing is not the platform itself but the way it is configured. Businesses using public clouds should treat configuration review as a routine discipline, not a one-time project.
Continuous Monitoring and Threat Detection
Continuous monitoring helps security teams spot trouble before it turns into a crisis. That includes watching for unusual logins, privilege escalation, data movement, failed authentication patterns, configuration drift, and abnormal behavior across workloads and services. For organizations depending on a cloud computing service for daily operations, continuous monitoring supports faster response, cleaner audits, and better decision-making. It is also essential for protecting data centers, distributed applications, and business records as computing power and cloud dependence continue to grow.
Conclusion: Secure Your Cloud Before Data Loss Happens With Q-Tech Inc.
The cloud can help businesses move faster, scale smarter, and serve customers better, but only when security is treated as part of operations, not an afterthought.
Strong IAM, multi-factor authentication, encryption, data loss prevention, logging, patching, cloud backup and recovery, and implementing zero trust all work together to reduce data loss risk. At Q-Tech Inc., we help businesses strengthen their cloud environment with practical strategy and real protection. If your organization wants to improve resilience, protect sensitive information, and align with modern cloud security expectations, now is the right time to secure your cloud before data loss forces the issue.




